In this article, we will understand the fundamentals of cybersecurity, information security, and network security.
Cybersecurity: Protecting the Digital Realm
- Cybersecurity is the protection of information that is stored, transmitted, and processed in a networked system of computers, other digital devices, and network devices and transmission lines, including the Internet.
- Cybersecurity protection ensures confidentiality, integrity, availability, authenticity, and responsibility. In Cybersecurity protection also includes organizational policies and procedures, as well as technological tools like encryption and secure communication protocols, are used to protect data.
- Information Security and Network Security are the subset of cybersecurity.
Information Security: Safeguarding Data Integrity
Information Security is the security mechanism used to provide the confidentiality, integrity, and availability of information. Other qualities, like authenticity, accountability, nonrepudiation, and dependability also used to preserve the security of an information.
Network Security: Securing Digital Pathways
Network security is defined as the security mechanism used to protect networks and their services against illegal alteration, destruction and disclosure.
Objective of cybersecurity
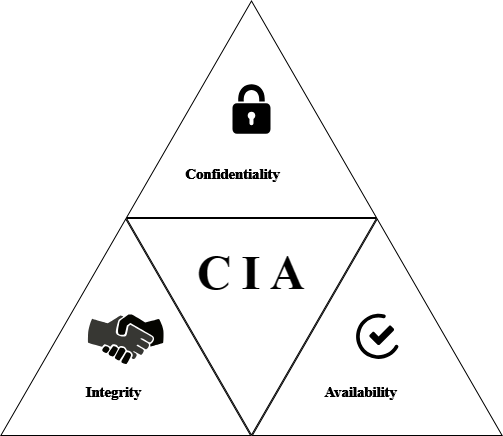
Cybersecurity encompasses three fundamental objectives at the core of information and network security: confidentiality, integrity, and availability. These objectives are collectively known as the CIA triad.
CIA triad embodies the fundamental security objectives for both data and for information and computing services..
Confidentiality
- Ensures only authorized access to sensitive information.
- Relies on data encryption to protect data from unauthorized disclosure.
- Implemented through access controls like user authentication and RBAC.
- Utilizes data masking techniques to hide sensitive information.
- Supported by legal measures such as NDAs to enforce confidentiality.
- A loss of confidentiality is the unauthorized disclosure of
- information
Integrity
- Maintains data accuracy and consistency throughout its lifecycle.
- Uses data validation techniques like checksums and hash functions.
- Manages version control for documents and software to track changes.
- Keeps access logs and audit trails for accountability and detection.
- Utilizes digital signatures to verify the authenticity and integrity of digital content.
- A loss of integrity is the unauthorized modification or destruction of information.
Availability
- Relies on redundancy to minimize downtime and ensure continuous access.
- Utilizes load balancing to optimize resource utilization and prevent overloads.
- Requires disaster recovery planning for quick restoration of operations.
- Leverages distributed systems architecture to reduce localized failures’ impact.
- Implements monitoring and alert systems for proactive maintenance
- A loss of availability is the disruption of access to or use of information or an information system.
While the CIA triad’s role in defining security objectives is well-established, to further enhancing the security strength of an information the additional concepts are necessary which includes Authenticity and Accountability
Authenticity
- It’s about being genuine, verified, and trusted, ensuring confidence in data or message validity.
- Authenticity Verify the user identities to confirm they are who they claim to be is a key aspect of authenticity.
- Authenticity ensures that every input received by the system originates from a trusted and authorized source.
- Helps establish trust in transmissions, messages, and their originators within a system or network.
- Critical for maintaining data integrity and preventing unauthorized access or tampering.
Accountability
- Accountability is a security goal that ensures actions are uniquely traceable to specific entities.
- Accountability supports non-repudiation, where parties cannot deny their actions or transactions.
- Aids in deterrence by holding individuals or entities responsible for their actions.
- Accountability facilitates fault isolation, helping identify and address issues quickly.
- Enables intrusion detection and prevention by attributing activities to accountable entities.
- Essential for after-action recovery, legal action, and forensic analysis in security incidents or transaction disputes.
